Trezor Bridge: A Secure Connection Between Your Trezor Wallet and Web Applications
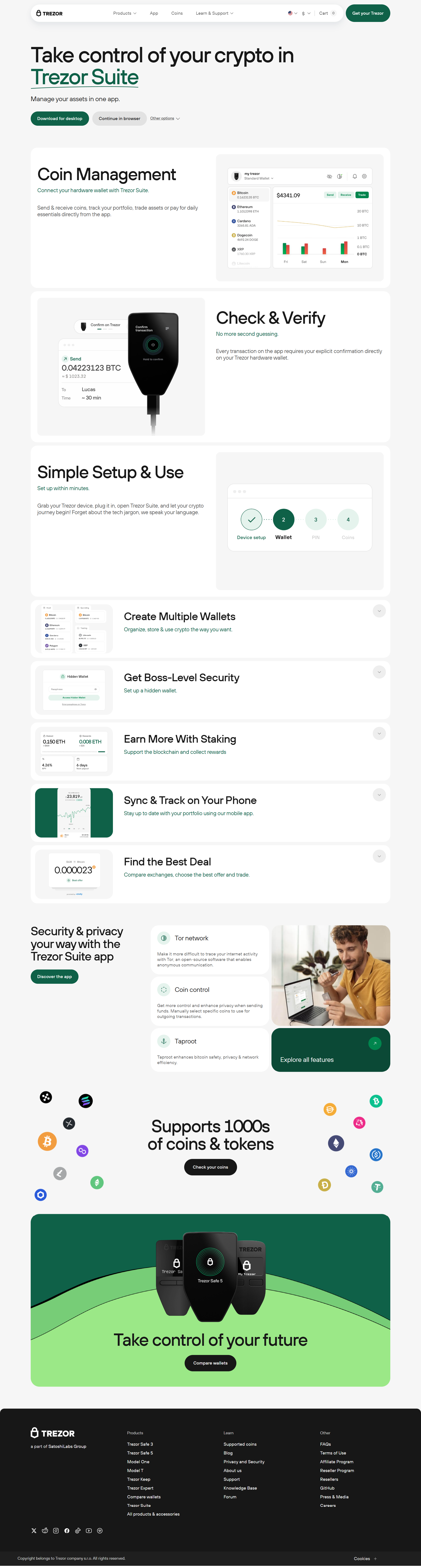
When it comes to securing your digital assets, the importance of a hardware wallet like Trezor cannot be overstated. However, managing cryptocurrency on a hardware wallet isn't always as seamless as using a regular online wallet. To bridge the gap between hardware wallets and web applications, Trezor Bridge was created. This software enables your Trezor hardware wallet to connect securely to various web-based platforms and decentralized applications (dApps), making it easier for you to manage your crypto holdings.
In this guide, we'll walk through what Trezor Bridge is, how to use it, and why it is an essential tool for anyone using a Trezor wallet to interact with web applications.
What is Trezor Bridge?
Trezor Bridge is a piece of software developed by Trezor that allows you to securely interact with web-based applications via your Trezor hardware wallet. It acts as a communication layer between your hardware wallet and the internet, enabling you to interact with various decentralized applications (dApps), cryptocurrency exchanges, and other web services.
With Trezor Bridge, your private keys remain securely stored offline on the Trezor device, ensuring that your cryptocurrency remains safe even when interacting with third-party services. It only facilitates signing transactions and data exchanges without exposing your sensitive information to online threats.
Why You Need Trezor Bridge
When managing cryptocurrencies, security is the top priority. While Trezor hardware wallets already provide robust security, Trezor Bridge ensures that you can use web-based services without compromising that security. Here’s why you need Trezor Bridge:
1. Secure Web-based Interaction
Trezor Bridge securely connects your Trezor wallet to various web-based services like MetaMask, MyEtherWallet, or DeFi platforms. This allows you to engage in transactions, staking, and token swaps while keeping your private keys protected and offline.
2. Offline Key Storage
Your private keys never leave the Trezor device, even when connecting to web applications. This feature helps protect your assets from hacking attempts or phishing scams targeting online wallets.
3. Support for Decentralized Finance (DeFi)
With the rise of DeFi applications, Trezor Bridge allows you to interact securely with platforms like Uniswap, Compound, Aave, and others without exposing your private keys. This integration makes Trezor Bridge a powerful tool for engaging in the growing decentralized finance ecosystem.
Setting Up Trezor Bridge
Setting up Trezor Bridge is straightforward and quick. Follow these steps to get started:
Step 1: Download Trezor Bridge
First, visit the official Trezor website at Trezor.io and navigate to the downloads section. Download the latest version of Trezor Bridge compatible with your operating system (Windows, macOS, or Linux).
Step 2: Install Trezor Bridge
Once the download is complete, open the installation file and follow the prompts to install Trezor Bridge on your computer. The software will run in the background and automatically connect your Trezor hardware wallet to web applications.
Step 3: Connect Your Trezor Wallet
Plug in your Trezor hardware wallet using the provided USB cable (or connect via Bluetooth if you're using the Trezor Model T). Once connected, Trezor Bridge will establish a secure link between your wallet and the browser-based applications you intend to use.
Step 4: Grant Web Application Access
After setting up Trezor Bridge, visit a supported web-based application like MetaMask or MyEtherWallet. You will be prompted to connect your Trezor wallet to the application. Confirm the connection on your Trezor device, and you are ready to interact with the platform.
Step 5: Approve Transactions
Any time you make a transaction, such as sending funds or interacting with a dApp, Trezor Bridge will send the transaction request to your Trezor wallet. You will need to approve the transaction on your Trezor device by confirming the details. This ensures that you retain full control over your crypto assets.
Trezor Bridge and Web3 Integration
One of the most significant advantages of Trezor Bridge is its seamless integration with the Web3 ecosystem. Here’s how Trezor Bridge works with popular Web3 applications:
1. MetaMask
MetaMask is one of the most popular Ethereum-based wallet extensions. Trezor Bridge allows you to use your Trezor device with MetaMask to sign Ethereum transactions securely. Once connected, MetaMask will display your Ethereum address, and you can sign transactions with your Trezor device, keeping your private keys offline at all times.
2. MyEtherWallet (MEW)
MyEtherWallet is another widely-used interface for managing Ethereum and ERC-20 tokens. By using Trezor Bridge, you can connect your Trezor wallet to MyEtherWallet and sign transactions directly on the Trezor device. This eliminates the need to expose your private keys while interacting with Ethereum-based applications.
3. DeFi Platforms
Engaging with DeFi platforms has never been more popular. Trezor Bridge enables users to interact with platforms such as Uniswap, Sushiswap, and Compound while ensuring their assets are secured on the Trezor hardware wallet. Transactions are signed offline, providing enhanced protection from malicious actors.
4. NFT Marketplaces
With the rise of NFTs (Non-Fungible Tokens), Trezor Bridge allows users to interact with NFT marketplaces like OpenSea and Rarible while keeping their private keys offline. You can mint, buy, or sell NFTs with the confidence that your funds are secure on your Trezor device.
Key Features of Trezor Bridge
- Secure Transaction Signing: Trezor Bridge only facilitates transaction signing. Your private keys remain safely offline on your Trezor device, ensuring that no sensitive data is exposed during transactions.
- Web3 Compatibility: Seamlessly interact with DeFi platforms, NFT marketplaces, and Ethereum dApps.
- Cross-Platform Support: Trezor Bridge is available for Windows, macOS, and Linux, making it accessible to a wide range of users.
- User Control: Every transaction requires your confirmation on the Trezor device, giving you full control over your crypto holdings.
Best Practices for Using Trezor Bridge
1. Always Use Trusted Platforms
While Trezor Bridge helps secure your interactions, always ensure that you are using trusted platforms and verify the URLs before connecting your Trezor device. Phishing scams can deceive users into connecting their wallet to malicious sites.
2. Keep Your Recovery Phrase Safe
Your recovery phrase is the key to restoring your wallet if it is ever lost or damaged. Store it offline in a secure location and never share it with anyone.
3. Regularly Update Firmware
Ensure that your Trezor device has the latest firmware updates. Trezor regularly releases updates to improve security and add new features, which help protect your assets.
Conclusion: Secure Your Crypto with Trezor Bridge
Trezor Bridge is a crucial tool for securely interacting with web-based services while keeping your Trezor hardware wallet and private keys offline. Whether you’re managing tokens, trading on DeFi platforms, or engaging with NFT marketplaces, Trezor Bridge allows you to do so with confidence, knowing your assets are safe from online threats.
By using Trezor Bridge alongside your Trezor wallet, you can enjoy the benefits of a connected cryptocurrency experience while ensuring that your funds remain secure. Download Trezor Bridge from the official Trezor.io website today and take your crypto security to the next level!